Keep What Matters: Privacy, Sync, and Portability for a Living Knowledge Archive
Your notes, bookmarks, and research deserve to outlast devices, apps, and trends. Today we explore Privacy, Sync, and Portability as practical disciplines for safeguarding a personal knowledge archive over time, blending cryptography, resilient workflows, and humane habits so your ideas travel safely, remain searchable, and stay yours forever.
Start Strong: Formats, Structure, and Names That Age Well
Longevity begins with small, consistent choices. Prefer human-readable, well-documented formats that remain useful even when tools disappear. Name files for context, not convenience. Organize in ways your future self understands after a long break. Structure your archive to welcome migrations, collaboration, and graceful evolution without frantic conversions or brittle dependencies.

Privacy By Design: Protect The Sensitive, Minimize Exposure
Assume devices get lost, accounts are breached, and networks leak. Build from least privilege outward, encrypt before syncing, and separate sensitive material from casual notes. Reduce data exhaust, disable unnecessary telemetry, and keep private indexes local. With forethought, you can collaborate, search, and publish while keeping your most personal knowledge truly yours.
Local-First, End-To-End, And Calm By Default
Prefer tools that work offline, save locally, and only sync encrypted blobs. End-to-end encryption with audited primitives like XChaCha20-Poly1305 or AES-256-GCM preserves confidentiality even if servers misbehave. Keep plaintext keys off cloud drives, and verify that search uses local indexes so queries never reveal sensitive context to third parties.
Key Hygiene, Passphrases, And Hardware Backups
Use long passphrases, argon2id for derivation, and hardware keys where feasible. Store printed recovery codes in separate, sealed locations. Rotate secrets on a schedule you can remember, and document your process. A simple laminated card with instructions has rescued many tired travelers after a misplaced laptop or a corrupted phone backup.

Know Your Model: Files, Databases, And Hybrids
File-based sync with tools like Syncthing or rsync is transparent but needs discipline. Database-driven sync may be faster, yet debugging conflicts can be harder. Hybrids offer local indexes over plain files. Pick according to scale and comfort, and keep an escape hatch that lets you export everything without opaque steps.
Conflicts Happen: Plan The Merge
Conflicts are design questions, not accidents. Vector clocks, CRDTs like Automerge, or Git-style merges each shine in different contexts. Establish predictable rules: you keep both edits, annotate differences, and notify yourself. Tests with deliberate collisions build confidence, so disagreements become opportunities to learn, not silent data loss.
Test Like A Traveler, Not A Lab

Go offline for a day, edit on multiple devices, attach images, and then reconnect. Intentionally rename folders and move files during sync windows. Review logs, compare checksums, and confirm backlinks survive. A weekend chaos rehearsal now prevents a weekday panic later. Share your best experiments so others can copy them.
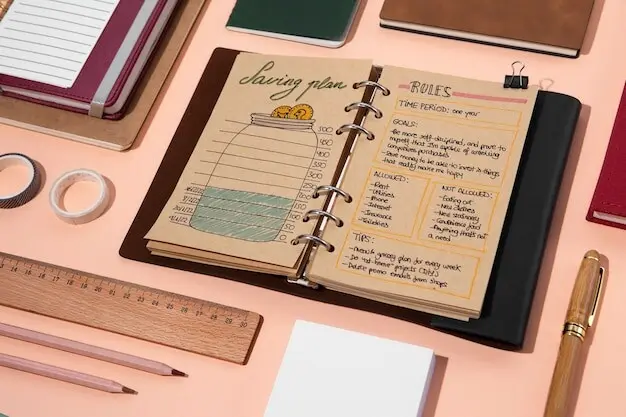
Portability And Exit Plans: Leave Whenever You Want
Portability means you can migrate on your terms. Prioritize open formats, documented APIs, and routine exports with checksums. Keep a manifest that lists locations, indexes, and dependencies. Schedule periodic drills converting a subset with pandoc or scripts. When tools change, you spend minutes deciding, not months untangling.
Backups, Integrity, And Time: Practicing The Return
Backups matter only when restores are easy. Follow the 3-2-1 pattern, store at least one copy offline and one immutable, and verify with checksums. Schedule rehearsal restores and record lessons learned. An archive that survives decades is built from quiet, dependable routines you barely notice keeping watch every day.


Habits, Community, And Continuity
Tools help, but habits endure. Capture small thoughts daily, review weekly, and refactor gently. Write down conventions so your future self or trusted partner can maintain continuity. Share lessons with peers, ask questions, and subscribe for deep dives. Knowledge gardens thrive when gardeners trade seeds, stories, and resilient routines.